Windows Kernel Exploitation Tutorial Part 8
In Summary : The analysis part on this vulnerability is a multi-step breakdown of different functions used in the UseAfterFree.c file. ...
https://updatesinfosec.blogspot.com/2018/05/windows-kernel-exploitation-tutorial.html
In Summary :
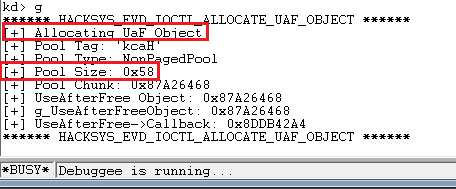
The analysis part on this vulnerability is a multi-step breakdown of different functions used in the UseAfterFree.c file. Just reading through the file gives us 4 different functions, that seems useful to what we have to analyze here. We’d look into each of the functions one by one below[...]
kindly refer the following link as follow up :
https://ift.tt/2rahdem
Submitted May 01, 2018 at 09:37AM by TechLord2
via reddit https://ift.tt/2jlKnDl
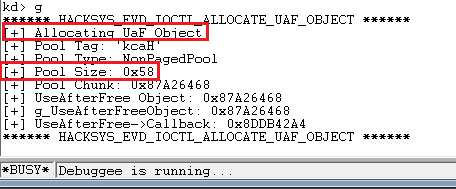
The analysis part on this vulnerability is a multi-step breakdown of different functions used in the UseAfterFree.c file. Just reading through the file gives us 4 different functions, that seems useful to what we have to analyze here. We’d look into each of the functions one by one below[...]
kindly refer the following link as follow up :
https://ift.tt/2rahdem
Submitted May 01, 2018 at 09:37AM by TechLord2
via reddit https://ift.tt/2jlKnDl